Online flight tracking reminds us that the secretive EO-5Cs regularly fly along the border between North and South Korea.
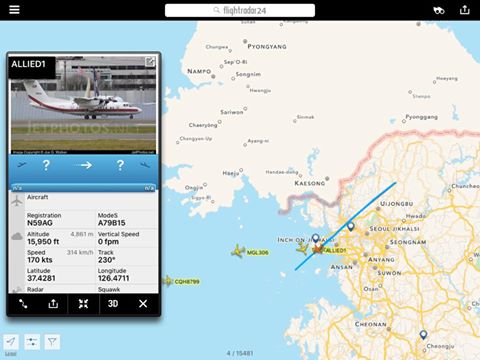
The above screenshot was taken from Flightradar24 by Guglielmo Guglielmi, an expert in online flight tracking.
It shows a U.S. Army Dash 7 surveillance aircraft, designated EO-5C, during a mission south of the Korean Demilitarized Zone.
Three such Army aircraft packed with sensors, known as ARL (Airborne Reconnaissance Low), are believed to be stationed in South Korea. The aircraft don’t wear military markings but carry a civil registration (in this case N59AG) to disguise their real mission and some of their sensors can be retracted making the airplanes more similar to a regional liner rather than a special operations asset involved in a clandestine mission.
The EO-5C can detect and fix enemy transmissions on all the radio spectrum, collect both IR (Infrared) and visibile-light very high-resolution imagery, track moving ground targets as well as detect and monitor specific features of the ground below: capable to determine how footprints in the sand change over time, the ARL is believed to be used in Korea to hunt for Pyongyang‘s underground tunnels/facilities.
The Army has deployed the first of these ISR (Intelligence Surveillance Reconnaissance) planes to the Korean Peninsula in 1996. An EO-5C could be frequently monitored on FR24 flying from Crete to Libya to perform intelligence gathering activities in North Africa until it was replaced by another special plane: an ATR-42.
Once again it’s worth mentioning that a spook plane flying a reconnaissance mission in theater should not be trackable online using a web browser….
Top image, FR24 via Guglielmo Guglielmi. Bottom image: U.S. Army.
Related articles