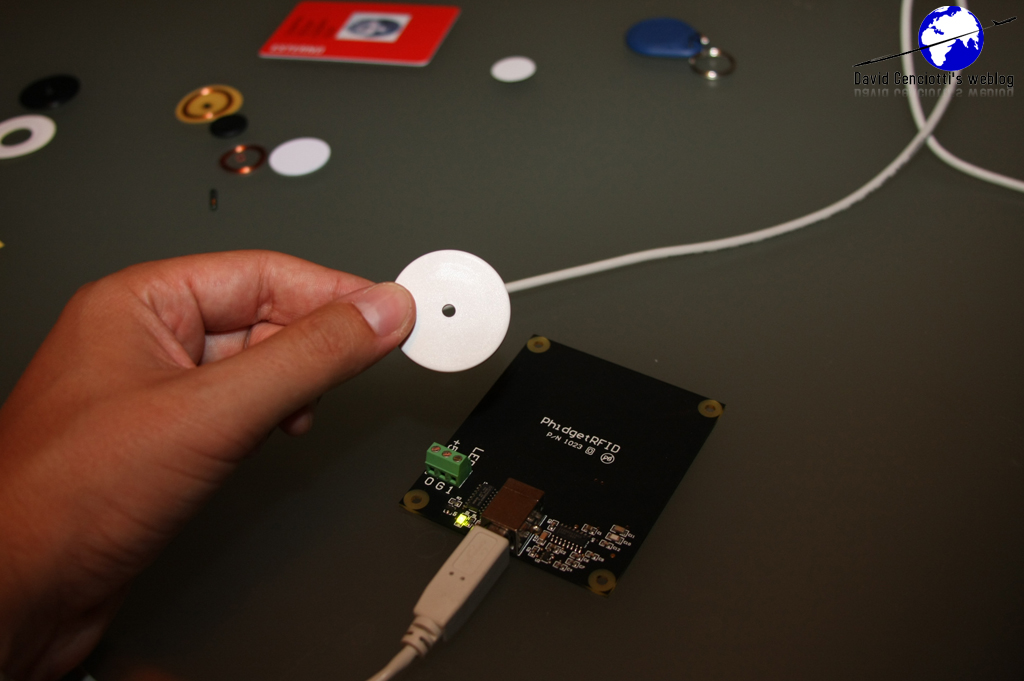
Eurocopter and Telit recently signed a contract according to which, Telit RF Technology will develop a wireless communication system to monitor helicopters critical systems and to improve aircraft maintenance. According to the information that have been released so far, each critical system/part will be monitored using an Active RFID tag. The tag will be used to store the current status of the part, (most probably) the maintenance checks’ expiration dates, the date of the last check, and so on. The information will be transmitted to a Back End server where an application will correlate the data providing a means to monitor the status of the entire helicopter using the radiofrequency. Unfortunately, the news doesn’t provide any more detail dealing, for example, with the way the communication between tag and the reader will be secured and how the Back End system is going to be protected from hackers’ attacks. I’m a worrying for nothing? Probably. In my experience (I also wrote my graduation thesis on RFID security) security matters are underestimated when implementing RFID solutions. However the risk is extremely high for many reasons. First of all, because, being not as spread as other very well know technologies, RFID is hacked only by skilled people whose probability to cause significant damage is extremely high. Many tend to think that RFID is a safe technology just because only a few know exactly how a transaction between a reader and a tag works. Lack of “security awareness” aside, security countermeasures cost and make tags more expensive (thus render the solution less convenient). Security countermeasures like encryption or authentication require more power, more memory, more space on the tag to accomodate processors and memories able to perform crypto funcions and, consequently, more money. But the risk is extremely high. Just think to the following scenarios:
1) a DoS (Denial of Service) on the reader prevents the internal system from collecting information transmitted by the tag (leaving the Back End application “blind” and unable to perform the typical monitoring functions)
2) malware is injected by a rogue R/W tag to the reader to attack the Back End database or application, to gain unauthorized access to the internal network, to spread a virus, etc.
3) a cloned tag with wrong data (expiration dates, performed checks etc) can be used to provide a false information to the Back End system leading to an aviation safety risk (or disaster).
There are many more and the previous ones were interesting only to show the different risks embedded with Radio Frequency IDentification.
We currently don’t know the countermeasures that were thought to prevent the above theoretical risks from becoming real information or aviation incidents in the Telit – Eurocopter solution. However, just to provide an idea, of the technical measures required to secure an RFID solution and to improve the data security (and the aviation safety in this specific case), as an Information Security expert I will provide a list of the countermeasures aimed to prevent Integrity, Confidentiality and Availability of information (i.e. data) from being compromised (for more information on the attributes I suggest reading: About the hack into the F-35 Lightning II JSF (Joint Strike Fighter) project
- Mutual Authentication between tags and readers (to be sure that the information are transmitted to valid readers or received by valid tags)
- Frequency Hopping Spread Spectrum systems with multi-frequency tags (in order to switch on another frequency if the channel is saturated by jamming)
- Redundant architecture without any SPF (Single Point of Failure): in order to ensure “business continuity”
- Shielding of the components
- Physical protection of the readers
- PUF (Physically Unclonable Functions) as private keys for a challenge-response process
- Roles segregation with Least Privilege access
- Middleware code review
- Input validation before connecting to the DB
- Network separation by means of Application Gateway Firewalls
- etc.








