Five years ago today the raid that exposed the Stealth Black Hawk helicopter
Operation Neptune's Spear exposed the existence of the MH-X Stealth Black Hawk…
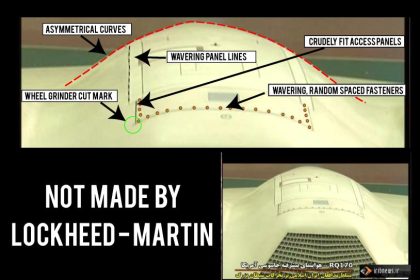
Unknown hatch on captured U.S. stealth drone raises questions
The amout of contribution I receive each time I publish a blog…
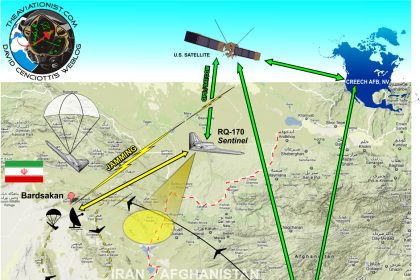
Infographic: how the U.S. top secret stealth drone was captured by Iran
Even if the story that the U.S. stealthy RQ-170 Sentinel drone captured…
Captured U.S. stealthy drone was hijacked exploiting GPS vulnerability. But hack description does not solve the mystery
Eventually there is an explanation for the mysterious capture of the U.S.…
"Three U.S. and four Israeli drones captured in Iran to be put on display soon": Tehran Times says. "Downed" RQ-170 saga continues
Tehran Times reported that Iran is about to put on display "foreign…
How many U.S. stealthy drones were actually lost in Iran? New theories about the "downed" RQ-170 surface
Iran will clone and maybe improve the U.S. RQ-170 drone captured on…