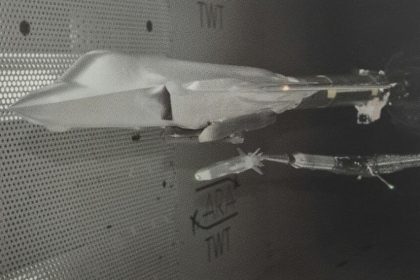
Photo shows F-35 SOM-J Air-Launched Cruise Missile separation tests in wind tunnel
Turkish air-launched cruise missile is being tested for integration on the F-35…
[Photo] All three F-35 variants fly together for the first time
F-35A, F-35B and F-35C Joint Strike Fighters flying together. A nice photo…
Photo shows F-35A fitted with two externally mounted Joint Strike Missiles
Last week the Norwegian Crown Prince visited Lockheed Martin’s Ft Worth facility…
Upgraded F-35 Block 2A Joint Strike Fighters delivered to the U.S. Air Force. Still much to do, though.
The brand new Joint Strike Fighters reached the 58th Fighter Squadron on…
Video: F-35A night refueling
Just released by Lockheed Martin, a short but interesting video showing the…
Exclusive Infographic: all Cyber Attacks on Military Aviation and Aerospace Industry
2011 has been an annus horribilis for information security, and aviation has…