A Rare Look at the Secretive RQ-170 Operations at Creech Air Force Base
A newly released video shows RQ-170 Sentinels at Creech Air Force Base,…
Satellite caught a U.S. RQ-170 Sentinel stealth drone on the ground at Creech AFB
One of our readers has spotted something interesting in a satellite image…
UK flying its MQ-9 Reaper UAVs from RAF Waddington as well as from Creech AFB, Nevada
British media outlets are reporting that the Royal Air Force is now…
Exclusive Infographic: all Cyber Attacks on Military Aviation and Aerospace Industry
2011 has been an annus horribilis for information security, and aviation has…
A Sukhoi Su-27. At Creech Air Force Base, Nevada.
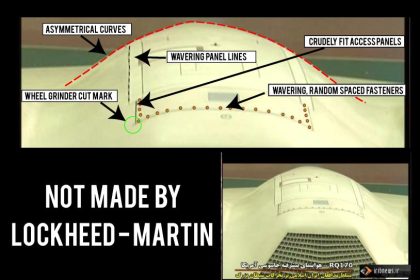
Update, Jan. 11 13.00 GMT Look at the following image Lazygranch.com has…
Unknown hatch on captured U.S. stealth drone raises questions
The amout of contribution I receive each time I publish a blog…