Latest Information Warfare News
Let’s Talk About The Digital Evolution Of Electronic Warfare
How the rapid increase in computing power and affordability of advanced technologies…
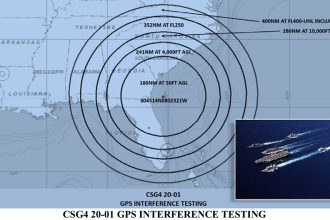
U.S. Navy Now Jamming GPS Over Six States and 125,000 Square Miles.
FAA Issues Advisory for Pilots: Large Military GPS Jamming Exercise in Southeast.…
Iran Begins Cyber Attacks Against U.S. Government Websites, Leaves Nuclear Deal.
Raft of Low Level Attacks Defaces Home Pages and Brings Down Websites.…
Vulnerable To Cyber Attacks, ADS-B May Expose F-22s To Web Based Tracking GAO Warns
A new report highlights the risks of ADS-B transponders. But it focuses…
See How USAF Aggressors Jam Civilian GPS Signals in Training at Nellis Air Force Base
GPS Jamming is a New Story from Red Flag 18-1, But We…
Turkish Blackhawk Kill Claimed by Kurds on YouTube, Turks “Counterattack” on Twitter.
The Social Media Battlefield: Fighting a Confusing War on Twitter, Youtube and…