MQ-9 Reaper Gets New Capabilities Against Cyber And Anti-Aircraft Threats
The MQ-9s of USSOCOM and AFSOC will get cyber anomaly detection and…
Let’s Talk About The Digital Evolution Of Electronic Warfare
How the rapid increase in computing power and affordability of advanced technologies…
The Amazing Growler Ball 2020 Video Teases An EA-18G Cyber Attack Capability That Is Yet To Come
This year's Growler Ball provides an opportunity to discuss the EA-18G's ability…
Let’s Forget The Hype And Talk About The AI vs Human Pilot Simulated Dogfight
The Falcon AI agent managed to defeat the human pilot with an…
Cybersecurity In The Sky: Internet of Things Capabilities Making Aircraft More Exposed To Cyber Threats Than Ever Before
The rise of IoT (Internet Of Things) could become a security nightmare…
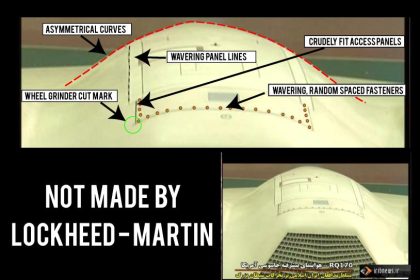
Middle East Cyber War: Revenge Of The Drones
In the same hours in which I was publishing my post on…