The WH and the Pentagon have a plan to step up offensive cyber operations to deter foreign adversaries.
The Trump administration has authorized the use of “offensive cyber operations” as part of a new national cyber strategy that aims at deterring attacks on the U.S. most critical networks, preventing interferences on future elections (in order to avoid a 2016 DNC hack) and face a wide array of intrusions, ranging from criminal activity to cyber espionage.
According to national security adviser John Bolton, the new policy will ease the rules on the use of cyber weapons to protect the nation and includes a new classified presidential directive that replaced one from the Obama administration.
According to the Washington Post, “In general, the president’s directive — called National Security Presidential Memorandum 13, or NSPM 13 — frees the military to engage, without a lengthy approval process, in actions that fall below the “use of force” or a level that would cause death, destruction or significant economic impacts, said individuals familiar with the policy who spoke on the condition of anonymity to discuss nonpublic information.”
Most analysts believe the strategy does not differ too much from the Obama administration’s cybersecurity national action plan (CNAP) issued in 2016; the problem, according to some former officials “was not the policy, but the inability fo agencies to deliver a forceful response.”
Obama’s CNAP included a series of near-term initiatives to enhance cybersecurity capabilities within the Federal Government and across the country, that included partnering with leading technology firms and financial companies (“Cyber Security Alliance”), investment of over 19B USD in President’s FY 2018 budget (a 35% increase from FY16), research and development around commonly used “utilities” such as open source software, protocols and standards.
Earlier this week, the DoD released a cyber strategy document that points towards China and Russia as the United States’ top adversaries and focuses on deterrence: among the ingredients for succeeding in tomorrow’s cyberspace, the Pentagon report lists Innovation, Agility, Automation and Data Analysis as well as COTS (Commercial-Off-The-Shelf) capabilities. “The Department will counter cyber campaigns threatening U.S. military advantage by defending forward to intercept and halt cyber threats and by strengthening the cybersecurity of systems and networks that support DoD missions. This includes working with the private sector and our foreign allies and partners to contest cyber activity that could threaten Joint Force missions and to counter the exfiltration of sensitive DoD information.” Key to defending US interests in the cyberspace will be the resilience of U.S. critical infrastructure: the Pentagon plans to counter attacks on critical networks and systems mainly by improving public-private information-sharing mechanisms.
Furthermore, the 2018 DoD strategy calls for cultivating talents, expanding crowd-sourced vulnerability identification and shorter hardware and software procurement times in order to keep pace with the rapid advance of technology.
This is what this author wrote last year commenting the impact of new technologies and digital transformation on the military:
“The impact of “pervasive technologies” on today’s society is often referred to as “Digital Transformation,” part of the so-called “Revolution 4.0,” where fusion of technologies is blurring the lines between the physical, digital, and biological spheres.
For instance, when it deals with the militaries, today’s joint operations on the battlefield require reliable information gathered through a wide variety of sensors aboard drones, spyplanes or provided by troops operating in the field around the world to decision makers oceans apart.
[…] while a large mix of digital technologies is making the world fully connected to improve collaboration, learning, information sharing and decision-making, companies around the world continue to invest in research and development and seek new technologies that can give them an advantage on their market. More or less what their old and new “enemies” are doing, at the same speed, or faster.
Moreover, a growing reliance on technology implies new advanced adversaries to face: in fact, the so-called Revolution 4.0 has already completely changed the geopolitical landscape requiring Defense and National Security to evolve and include the Cyber domain because even smaller economies, organizations or individuals (backed by some intelligence service or not) can pose a significant threat to larger nations today.
Attackers have been trying to intrude Government and Private Sector’s firms’ networks, often with real cyber weapons, for years. “Software-based” weapons systems, IoT capabilities, Big Data, Cloud Computing and digitization will simply expand the attack surface they can target, making them even more aggressive and dangerous than ever before, also as a consequence of the speed of the 5G connectivity that will be the driver for more services as well as more powerful attacks. Therefore, a Cybersecurity strategy covering the whole technological domain will be the key to address new and existing risks and threats before these can give the enemy an edge both in the cyberspace and in the battlefield. And such strategy will not have to cover “defensive” cyber operations only but also “offensive” ones.”
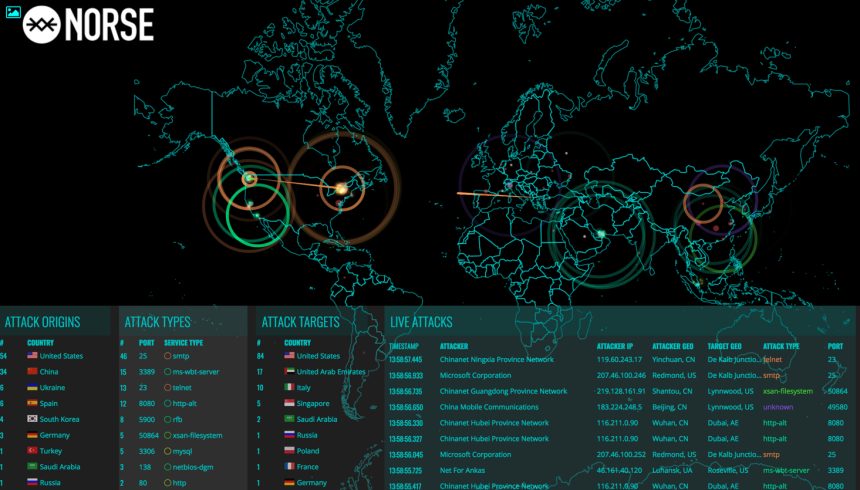
Top image credit: Norse